10 Best Third Party & Supplier Risk Management Software
Unexpected failures in supply chains and support vendors has the potential to cause irreversible damage to an organisation’s reputation and trust with both existing and prospective customers. Consequently, there is increased pressure on governance, risk and compliance professionals to demonstrate to executive teams why they must step-up and get a better handle on third-party risks as part of their broader risk framework.
So the Third-party risk management extends system vulnerability testing through to the providers of services, hardware, software, and applications that are used in infrastructure. That assessment also extends through to associate companies other than suppliers.
The Third-Party Risk Management Software can be deployed as a standalone product or as part of larger governance, risk, and compliance endeavor. Third-party and supplier risk management solutions must integrate with other software tools including supply chain suites, quality management software, ERP systems, and governance, risk, and compliance software if they are given separately.
The next step we will explain the best third and supplier risk mangement software
Top 10 Software
1. ONETRUST

OneTrust is defining an entirely new market category of software – the industry of trust – and the market is certainly responding.
now based in Atlantic , makes software for businesses trying to stay on the right side of the growing number of internet regulations. In response to the new California law, OneTrust made it easy for companies to set up a number to manage the requests.
In an attempt to rein in tech giants like Facebook and Google, governments around the world in recent years have approved new laws governing how websites must handle consumer data, treat their competitors and protect young people. The European Union has a data privacy law that governs the entire bloc. California has approved two privacy measures in recent years, and other states have followed suit.
2. UPGUARD

UpGuard provides cybersecurity risk management software (offered as SaaS) that helps organizations across the globe prevent data breaches by continuously monitoring their third-party vendors and their security posture. UpGuard is the only service that offers world-class data leak detection capabilities across an organization’s supply chain while continuously monitoring over a million companies to identify security exposures using proprietary security ratings proactively. Their expertise has been featured in The New York Times, The Wall Street Journal, Bloomberg, The Washington Post, Forbes, Reuters, and TechCrunch among others. UpGuard’s powerful risk assessment workflows enable organizations to automate security questionnaires, and the identified risks from responses are automatically mapped to vendors’ security ratings providing a holistic view of risks posed by third-party vendors. Its remediation capabilities make it easier for organizations to collaborate internally and with third-party vendors to remediate the identified security risks.
3. BITSIGHT
BitSight transforms how organizations manage cyber risk. The BitSight Security Ratings Platform applies sophisticated algorithms, producing daily security ratings that range from 250 to 900, to help organizations manage their own security performance; mitigate third party risk; underwrite cyber insurance policies; conduct financial diligence; and assess aggregate risk. BitSight’s solutions for Security Performance Management, Third Party Risk Management, Critical National Infrastructure, and Cyber Insurance are further bolstered by partnerships with Solactive, Refinitiv and Kovrr, broadening BitSight’s offerings for investors and cyber insurers as cybersecurity ratings continue to demonstrate a strong correlation to business performance. BitSight is the Standard in Security Ratings with over 2,400 global customers, including 20% of the Fortune 1000, and the largest ecosystem of users and information. The BitSight Security Rating was also used by 20% of the world’s governments in 2020 and is currently available on over 40 million organizations worldwide.
4. VENMINDER
Venminder is an industry recognized leader of third-party risk management solutions. Dedicated to third-party risk, the company is the go-to partner for software, high-quality assessments on vendor controls, certified subject-matter expertise and education.
Venminder’s platform provides a centralized location to execute a third-party risk management program. It enables users to store documentation, onboard a vendor, track contracts, manage SLAs, send and manage questionnaires, manage due diligence and oversight, complete risk assessments, create workflows, run reporting and more.
Assessments performed by Venminder’s qualified experts, including CISSPs, CPAs, financial risk analysts, paralegals and more, are readily available in an online library. The assessments enable clients to identify possible risks and understand areas of strength on their vendors’ information security and privacy standards, SOC reports, financial viability, business continuity/disaster recovery preparedness, contractual standards, regulatory compliance and more.
Venminder clients also use the firm to streamline due diligence processes by outsourcing vendor document collection; and regularly consult with Venminder’s experts to ensure their third-party risk management policy and procedures meet industry standards. The Venminder platform is used by 1,000+ customers across a wide range of industries to execute their third-party risk management programs. As the company’s solutions are designed to accommodate growth and various levels of program maturity, customers range in size from small to Fortune 100 organizations.
As the industry’s go-to leader, Venminder’s team of highly experienced professionals regularly speak at conferences, provide the latest research and educational content, host CPE credit eligible webinars and provide access to an online networking community for third-party risk professionals, Third Party ThinkTank.
5. WHISTIC
Whistic simplifies how businesses assess, publish, and share security documentation with customers and vendors.
The Whistic Vendor Security Network accelerates the vendor assessment process by enabling buyers to access and evaluate a vendor’s Whistic Profile and create trusted connections that last well beyond the initial point-in-time assessment. Additionally, Whistic facilitates zero-touch assessments via the Whistic Trust Catalog which contains security information for more than 35,000 businesses. Make security your competitive advantage and join businesses like Airbnb, Okta, Betterment, Vonage, and Qualtrics who are leveraging Whistic to modernize their vendor security programs.
6. SECURITY SCORECARD
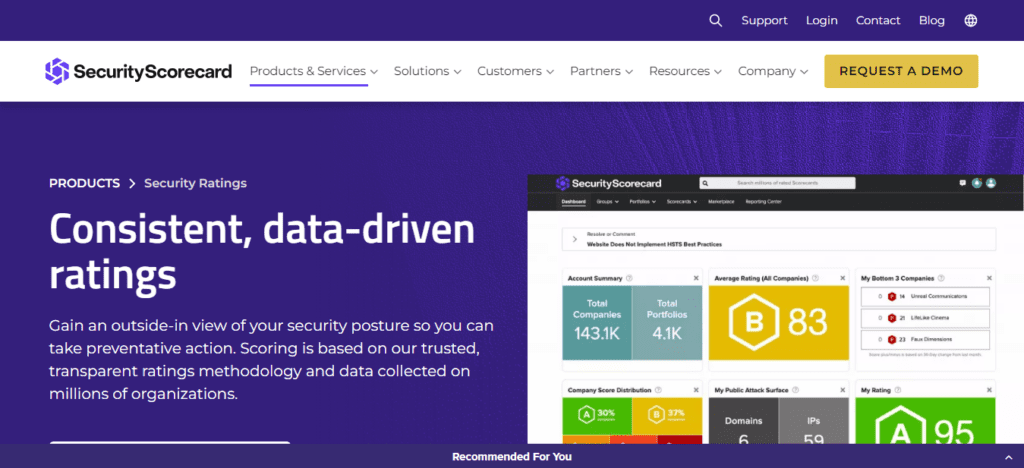
SecurityScorecard is the global leader in cybersecurity ratings with more than 12 million companies continuously rated. Founded in 2013 by security and risk experts Dr. Aleksandr Yampolskiy and Sam Kassoumeh, SecurityScorecard’s patented technology is used by over 30,000 organizations for enterprise risk management, third-party risk management, board reporting, due diligence, cyber insurance underwriting, and regulatory oversight. SecurityScorecard is the first cybersecurity ratings company to offer digital forensics and incident response services, providing a 360-degree approach to security prevention and response for its worldwide customer and partner base. SecurityScorecard continues to make the world a safer place by transforming the way companies understand, improve and communicate cybersecurity risk to their boards, employees and vendors. Every organization has the universal right to their trusted and transparent Instant SecurityScorecard rating.
7. CYBER GRX
CyberGRX is a SaaS platform whose mission is to help customers and the third parties with whom they do business solve the challenge of risk management. It is built on NIST-based assessments, mapped to the ISO 27001 framework and can be mapped to most other frameworks as well.
Onboarding vendors is simple with a search feature for checking if companies are already in the system, as well as for any previously conducted assessments. Several vendors can easily be onboarded at once with bulk import functionality.
Assessments have three tiers: Tier 1 provides the strongest level of due diligence while Tier 3 is the shortest-self assessment. Their offerings range from automated validation all the way up to onsite validation. If no tier is present, that means a community member has never performed an assessment on that company.
You can easily order an assessment at the appropriate tier level based on inherent risk. You can also submit special requests to the vendor. A lot of behind-the-scenes automation takes place once an order is submitted. Assessments are built with a great deal of logic, and the skip-level feature simplifies completion by jumping sections that are not applicable based on provided answers.
Business exposure is scored as low, medium or high risk and is determined by standardized questions that are not customizable. Users receive a report on the back end to show which controls matter most for remediation. Everyone’s progress is trackable.
The Portfolio Overview shows company statistics accompanied by a colorful bubble graphic that visualizes the likelihood of a cyber event. Circle sizes directly correlate to the likelihood of risk. The assessment is based on the user’s industry, current threat intelligence and a security ratings tool. Also shown are outliers with higher likelihoods of being attacked and their impacts.
CyberGRX built a table that outlines different controls and scores them on maturity (on a scale up to five) and effectiveness (on a scale up to 100). Comments are invited on the scores for enhanced collaboration. The Top Risks Chart ranks risks from low to high, prioritizing remediation with top suggestions for moving a company toward an acceptable posture. A variety of metrics can be added for company comparisons.
It appears the CyberGRX team is attempting to shift the industry away from an aggressive assessment approach to one more focused on collaboration. Basic, no-cost support is offered through 8/5 phone support. Overall, we found this to be an intuitive, simplified platform.
8. PROCESSBOLT

ProcessBolt empowers the enterprise supplier risk management process by replacing spreadsheets and emails with AI powered interactive questionnaires, process tracking, notifications, alerting, data driven dashboards and risk metrics.
Enterprise: Full visibility to supplier risk and assessment status.
Suppliers: Painless, intuitive and easilyrepeatable client risk assessments.
Risk Management Professional: One simple platform saving time and dollars.
Purpose built workflow to ease risk assessment process. Pre-configured and easily customizable assessment templates (BITS SIG, GDPR readiness, PCI SAQ, and more). Quickly attach evidence and artifacts to assessments. Meaningful notifications and alerts.
Second definition : ProcessBolt eliminates time-consuming manual risk assessment processes through automation so you can focus on your business, not data collection. ProcessBolt is the only complete vendor risk management solution on the market that serves both enterprises and vendors to maximize efficiency.
9. RECIPROCITY
The Reciprocity ROAR Platform unifies risk observation, assessment and remediation activities to provide a single, real-time view of risk and compliance in business context.
Using expert-provided guidance, easily create cyber assurance programs that unify compliance and risk to deliver a holistic, real-time view of your risk posture. The ROAR platform breaks down the silos that cause inefficiencies, gaps and blind spots and provides a single source of truth to increase efficiency, improve collaboration and optimize decision making.
A unified data model enables data sharing, eliminating redundant activities and minimizing audit fatigue. Automated workflows, pre-built integrations and flexible APIs free your staff from manual work while real-time alerts keep cross-functional teams informed. The ROAR platform delivers the expertise, guidance and insight you need, in the business context required, to maintain competitiveness, support growth and earn the trust of customers, partners and employees.
10. PREVALENT

Prevalent takes the pain out of third-party risk management (TPRM). Companies use our software and services to eliminate the security and compliance exposures that come from working with vendors, suppliers and other third parties.
Our customers benefit from a flexible, hybrid approach to TPRM, where they not only gain solutions tailored to their needs, but also realize a rapid return on investment. Regardless of where they start, we help our customers stop the pain, make informed decisions, and adapt and mature their TPRM programs over time.
Conclusion
To do this well you will need a cloud-based integrated platform you can trust, in order to deliver the visibility needed to determine a robust risk posture for effective third-party risk management.
Now that you have all the details of each, evaluate your business requirements, and choose the best software.





